Cryptogram
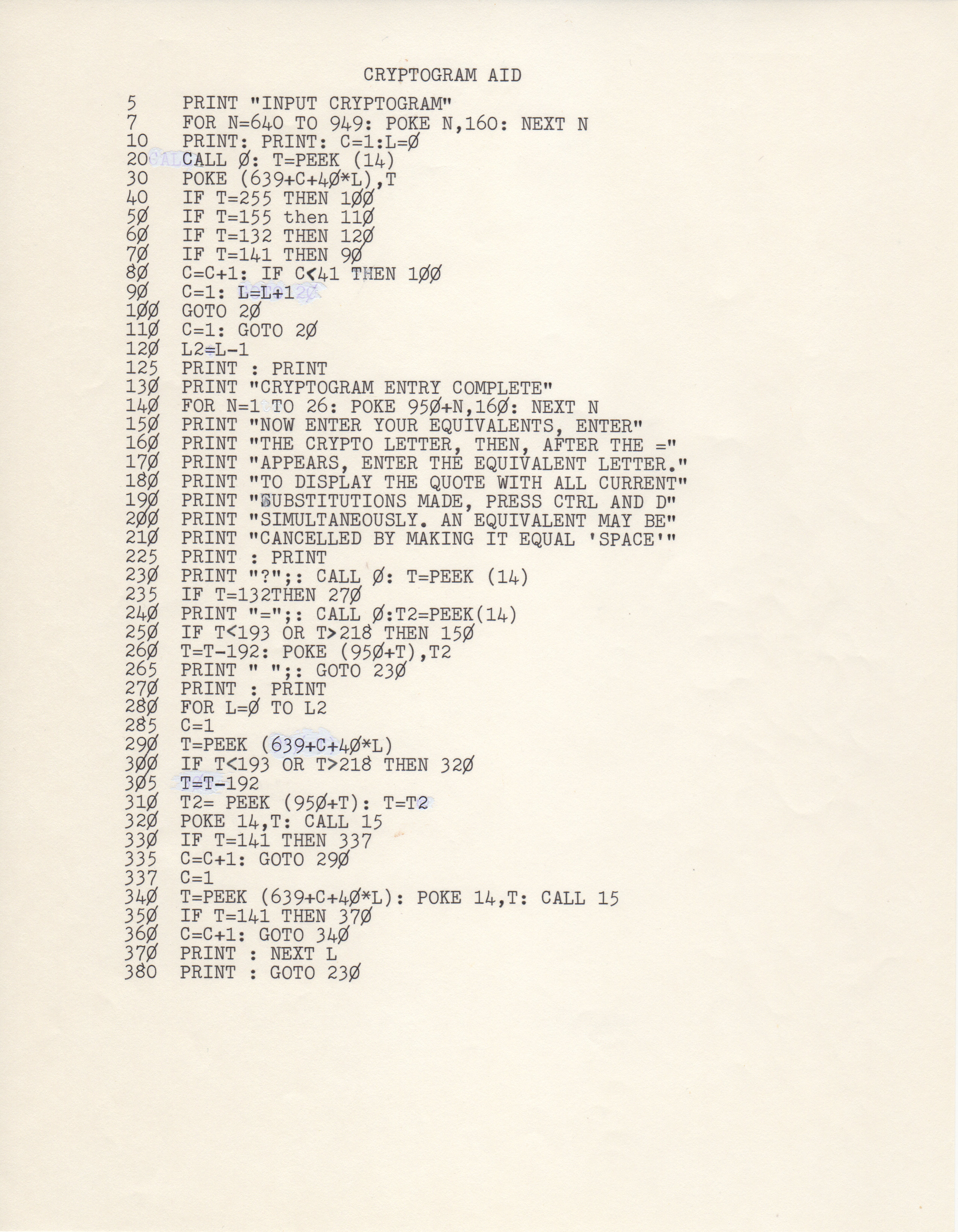
CRYPTOGRAM AID
5 PRINT "INPUT CRYPTOGRAM"
7 FOR N=640 TO 949: POKE N,160: NEXT N
10 PRINT: PRINT: C=1:L=0
20 CALL 0: T-PEEK (14)
30 POKE (639+C+40*L),T
40 IF T=255 THEN 100
50 IF T=155 then 110
60 IF T=132 THEN 120
70 IF T=141 THEN 90
80 C=C+1: IF C<41 THEN 100
90 C=1: L=L+1
100 GOTO 20
110 C=1: GOTO 20
120 L2=L-1
125 PRINT : PRINT
130 PRINT "CRYPTOGRAM ENTRY COMPLETE"
140 FOR N=1 TO 26: POKE 950+N,160: NEXT N
150 PRINT "NOW ENTER YOUR EQUIVALENTS, ENTER"
160 PRINT "THE CRYPTO LETTER, THEN, AFTER THE ="
170 PRINT "APPEARS, ENTER THE EQUIVALENT LETTER."
180 PRINT "TO DISPLAY THE QUOTE WITH ALL CURRENT"
190 PRINT "SUBSTITUTIONS MADE, PRESS CTRL AND D"
200 PRINT "SIMULTANEOUSLY. AN EQUIVALENT MAY BE"
210 PRINT "CANCELED BY MAKING IT EQUAL 'SPACE'"
225 PRINT :PRINT
230 PRINT "?";: CALL 0:T=PEEK(14)
235 IF T=132THEN 270
240 PRINT "=";: CALL :T2=PEEK(14)
250 IF T<193 OR T>218 THEN 150
260 T=T-192: POKE (950+T),T2
265 PRINT " ";: GOTO 230
270 PRINT : PRINT
280 FOR L=0 TO L2
285 C=1
290 T=PEEK (639+C+40*L)
300 IF T<193 OR T>218 THEN 320
305 T=T-192
310 T2= PEEK (950+T): T=T2
320 POKE 14,T: CALL 15
330 IF T=141 THEN 337
335 C=C+1: GOTO 290
337 C=1
340 T=PEEK (639+C+40*L): POKE 14,T: CALL 15
350 IF T=141 THEN 370
360 C=C+1: GOTO 340
370 PRINT : NEXT L
380 PRINT : GOTO 230
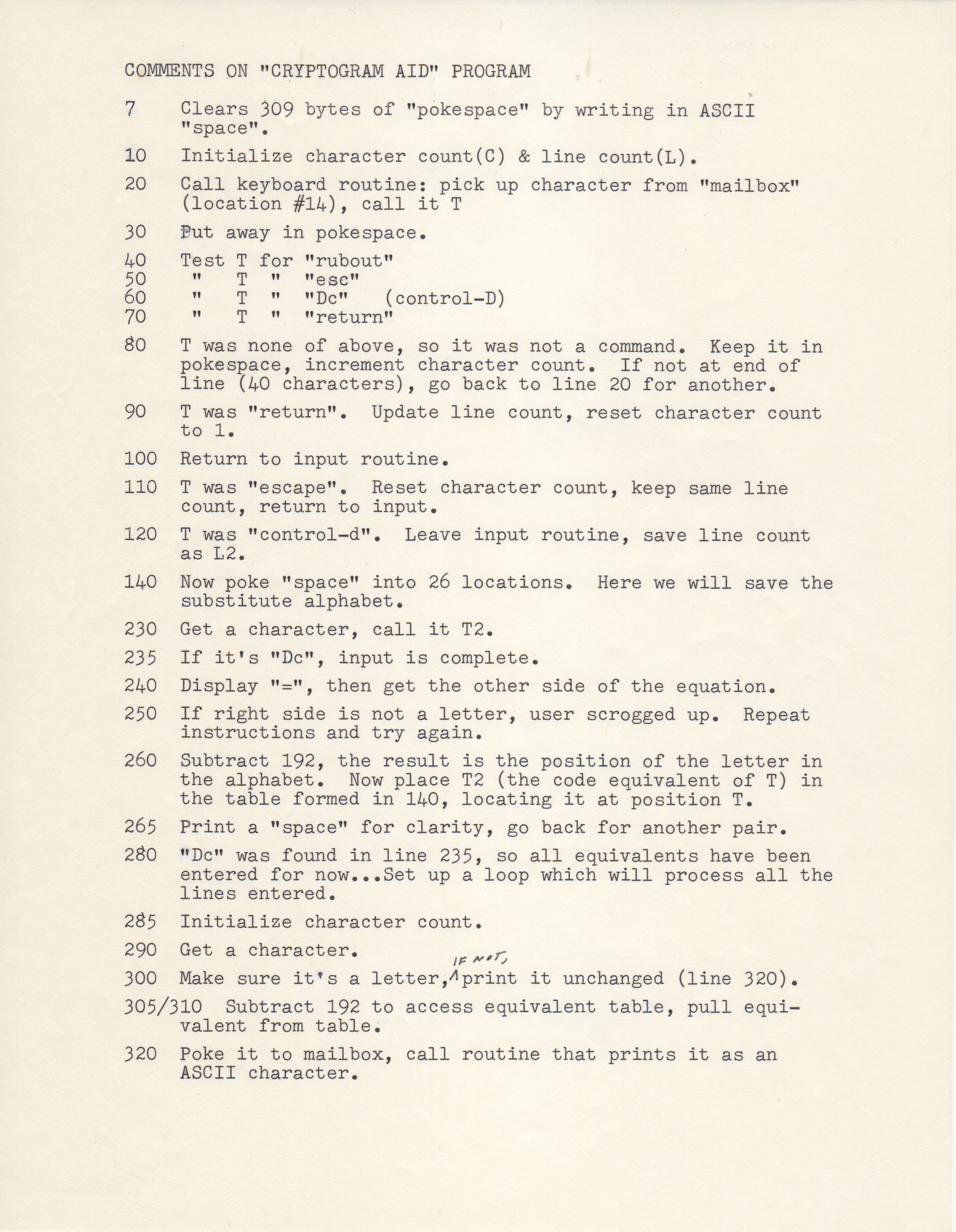
COMMENTS ON "CRYPTOGRAM AID" PROGRAM
7 Clears 309 bytes of "pokespace" by writing in ASCII
"space".
10 Initialize character count(C) & line count(L).
20 Call keyboard routine: pick up character from "mailbox"
(location #14), call it T
30 Put away in pokespace.
40 Test T for "rubout"
50 " T " "esc"
60 " T " "Dc" (control-D)
70 " T " "return"
80 T was none of above, so it was not a command. Keep it in
pokepsace, increment character count. If not an end of
line (40 characters), go back to line 20 for another.
90 T was "return". Update line count, resect character count
to 1.
100 Return to input routine.
110 T was "escape". Reset character count, keep same line
count, return to input.
120 T was "control-d". Leave input routine, save line count
as L2.
140 Now poke "space" into 26 locations. Here we will save the
substitute alphabet.
230 Get a character, call it T2.
235 If it's "Dc", input is complete.
240 Display "=", then get the other side of the equation.
250 If right side is not a letter, user scrogged up. Repeat
instructions and try again.
260 Subtract 192, the result is the position of the letter in
the alphabet. Now place T2 (the code equivalent of T) in
the table formed in 140, locating it at position T.
265 Print a "space" for clarity, go back for another pair.
280 "Dc" was found in line 235, so all equivalents have been
entered for now...Set up a loop which will process all the
lines entered.
285 Initialize character count.
290 Get a character.
300 Make sure it's a letter, if not, print it unchanged (line 320).
305/310 Subtract 192 to access equivalent table, pull equi-
valent from table.
320 Poke it tomailbox, call routine that prints it as an
ASCII character.
330 See if it was "return"
335 If not, increment character count & go get another.
337 It was "return", so reset character count.
340 We've printed all the equivalents that have been assigned
so far, now in lines 340 through 370, print the crypto-
gram line just under the letter equivalents that have been
assigned so far.
370 Go to next line & repeat the process.
380 All lines have been printed. Go to 230 to assign more
equivalents.
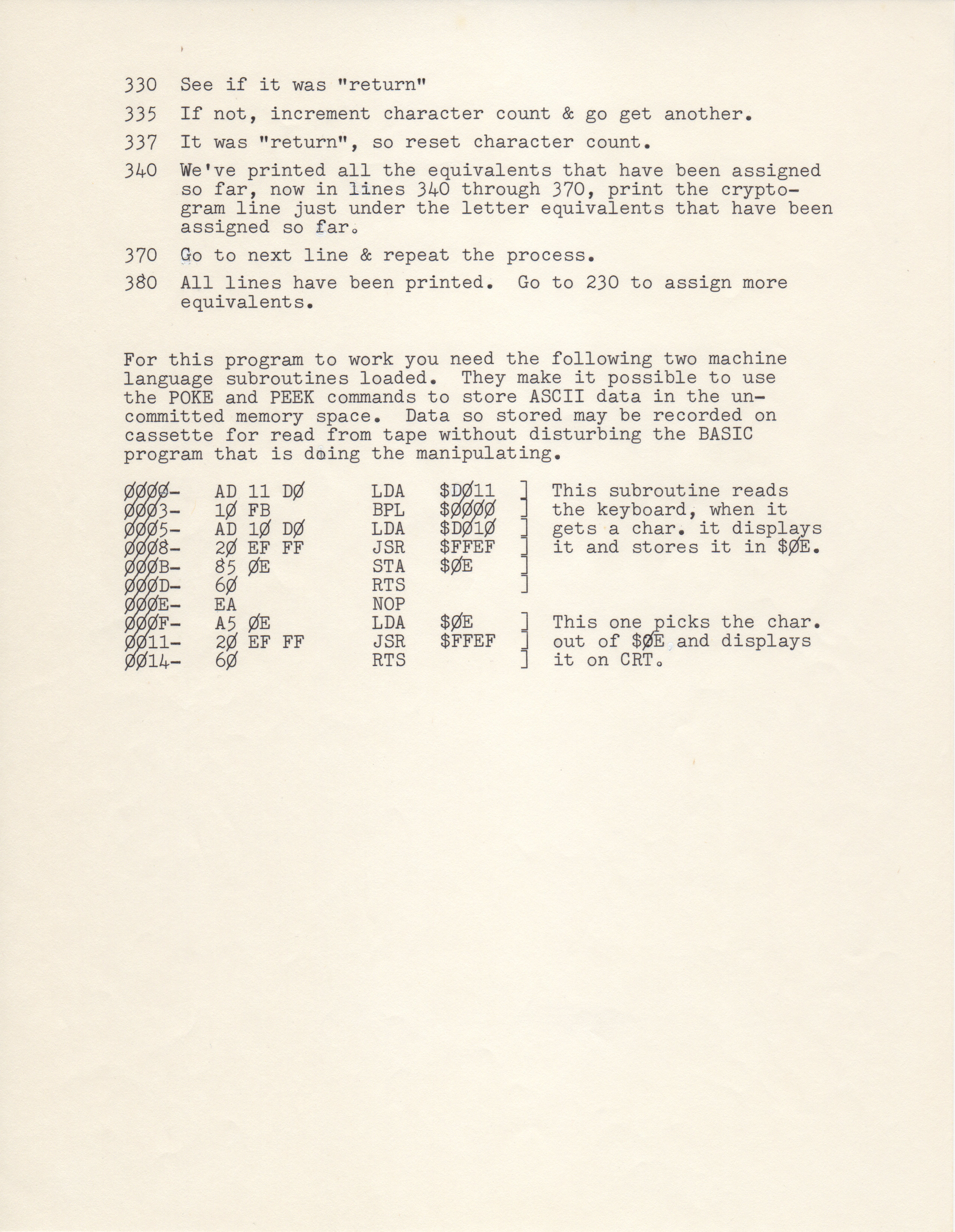
For this program to work you need the following two machine
language subroutines loaded. They make it possible to use
the POKE and PPK commands to store ASCII data in the un-
committed memory space. Data so stored may be recorded on
cassette for read from tape without disturbing the BASIC
program that is doing the manipulationg.
0000- AD 11 D0 LDA $D011 | This subroutine reads
0003- 10 FB BPL $0000 | the keyboard, when it
0005- AD 10 D0 LDA $D010 | gets a char. it displays
0008- 20 EF FF JSR $FFEF | it and stores it in $0E.
000B- 85 0E STA $0E |
000D- 60 RTS |
000E- EA NOP
000F- A5 0E LDA $0E | This one picks the char.
0011- 20 EF FF JSR $FFEF | out of $0E and displays
0014- 60 RTS | it on CRT.
- Printer-friendly version
- Log in to post comments